Midterm Exam Preparation Questions
期中代写 The purpose of these sample questions is to prepare you for success on the midterm exam. These questions have been used
Covers Lesson 1 through Lesson 6期中代写
The purpose of these sample questions is to prepare you for success on the midterm exam. These questions have been used on previous exams in this course, and represent the range of difficulty and depth you should expect on the actual midterm. You should expect some exam questions this semester to be similar to these questions, and some to be dissimilar.
We recommend that you use these questions as a companion to your lesson viewing sessions, and use them to help solidify your understanding as you progress through the course. This is generally more effective than reviewing these questions all at once just before the exam. We will release the solutions to these test preparation questions the week of the midterm exam.
Introduction to Software Analysis 期中代写
Question 1. Static vs. Dynamic Analysis
a.State one advantage of static analysis over dynamic analysis.
b.State one advantage of dynamic analysis over static analysis.
Question 2. We may classify each program as either safe or unsafe. For instance, we may say that a program is safe if it does not dereference a null pointer in any execution, and unsafe if there exists an execution in which it will dereference a null pointer.
A software analysis is considered sound if whenever it reports a program as safe,
the program is indeed safe. However, due to the undecidability of software analysis, a sound analysis may reject some safe programs. A sound analysis A is more precise than a sound analysis B if whenever analysis B accepts a program, analysis A also accepts that program.
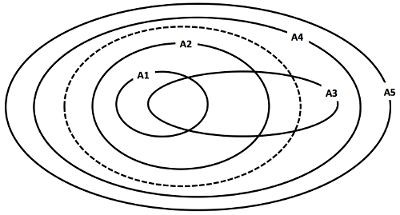
Consider the above figure. Inside of the dotted (—) oval lies the set of all safe programs, and the outside of the oval denotes the set of all unsafe programs. The inside of each solid oval, labeled A1 through A5, denotes the set of programs accepted by the corresponding analysis (e.g., these are five different null dereference checking analyses). Each analysis rejects all programs outside its corresponding oval.
Which of these five analyses are sound? List the sound analyses ordered by precision, i.e A6 > A7 > A8 indicates that A6, A7, and A8 are all sound, and A6 is more precise than A7, which is more precise than A8.
Introduction to Software Testing期中代写
Question 3. Consider a program P, and two test suites, X and Y for P. Test suite X covers set of branches Q in the program, while test suite Y covers set of branches R in the program. Suppose Q is a proper subset of R (Q ⊂ R). Which of the below statements are necessarily true?
AWhenever a test in Y reaches a statement, some test in X also reaches that statement.期中代写
B.Whenever a test in X reaches a statement, some test in Y also reaches that statement.
C.Test suite Y has strictly higher path coverage than test suite X.
D.Test suite Y has strictly higher branch coverage than test suite X.
Question 4. Consider the Java function:
void copy(int[] src, int[] dst, int N) { for (int i = 0; i < N; i++)
dst[i] = src[i];
}
Which of the below predicates is the function’s weakest possible precondition that prevent any null-pointer or array-out-of-bounds exceptions from being thrown?
NOTE: The expression X => Y is read: “X implies Y”. It is equivalent to (!X) OR Y.
A.N ≥ 0 ∧src != null ∧ dst != null ∧ N < src.length ∧ N < dst.length
B.N ≥ 0 ∧src != null ∧ dst != null ∧ N < src.length ∧ length = src.length
C.N > 0 ⇒(src != null ∧ dst != null ∧ N < src.length ∧ N < dst.length)
D.N > 0 ⇒(src != null ∧ dst != null ∧ N < src.length ∧ length = src.length
Question 5.期中代写
Consider a test suite consisting of three deterministic tests T1, T2, T3 for a correct program P. Since P is correct, it passes all the three tests. Suppose we have three mutants M1, M2, M3 of P such that: M1 fails T1 and T2; M2 fails none; and M3 fails T2 and T3.
Let M = P denote that M and P are equivalent. Likewise, let M != P denote that they are NOT equivalent.
a.Could it be possible that M1 = P? Justify your answer.
b.Mutation analysis will report M2 to the tester since it does not fail any test in the test suite. Which of the following actions are plausible for the tester to take given this information?期中代写
A.Determine if M2 == P, and if so, devise a new test case T4 on which M2 passes but P fails.
B.Determine if M2 != P, and if so, then ignore M2.
C.Determine if M2 != P, and if so, devise a new test case T4 on which P passes but M2 fails.
D.Determine if M2 == P, and if so, ignore M2.
Random Testing期中代写
Question 6. Consider the following concurrent program with two threads and shared variable x. Variables tmp1 and tmp2 are local to the respective threads. This program has a concurrency bug: it can lose an update to x.
Thread 1 Thread 2
1: tmp1=x 4: tmp2=x
2: tmp1=tmp1+1 5: tmp2=tmp2+1
3: x=tmp1 6: x=tmp2
a.Write one possible execution of the six statements that does not cause a concurrency bug.期中代写
b.Write one possible execution of the six statements that does trigger a concurrency bug.
c.What is the depth of the concurrency bug?
d.Specify the ordering constraints needed to trigger the bug.
Question 7.期中代写
Consider the following pseudo-Java function, in which HashMap<char,int> is used. A HashMap<K,V> is a data structure that associates a value of type V to a key of type K. The value v associated with a key k can be set with the API call put(k, v), and the value associated with the key k is returned by the API call get(k). For this problem, if no value has been associated with k, then assume get(k) returns 0.期中代写
double charRatio(String s, char a, char b) { int N = s.length();
HashMap<char,int> counts = new HashMap<char,int>(); for (int i = 0; i < N; i++) {
char c = s.charAt(i); int v = counts.get(c); counts.put(c, v+1);
}
return counts.get(a) / counts.get(b);
}
Describe how you could use a fuzzer to test this function. What bugs would you expect a fuzzer to identify in this function? What bugs would be more challenging for a fuzzer to identify? Explain your reasoning fully, including any assumptions you are making.
Automated Test Generation期中代写
Question 8. Consider the following class:
public class Lock {
private final static int UNLOCKED = 0; private final static int LOCKED = 1; private int state;
public Lock() { state = UNLOCKED; }
public void acquire() { assert(state == UNLOCKED); state = LOCKED; } public void release() { assert(state == LOCKED); state = UNLOCKED; } public int getState() { return state; }
}
Consider each of the below five tests individually. Answer whether that test can ever possibly be generated by Randoop. If yes, explain whether Randoop 1. Discards the test as illegal, or 2. Reports the test as a bug, or 3. Adds the test to components for future extension.
For simplicity,期中代写
assume that Randoop does not check for redundancy, and that the contracts it checks (not shown for brevity) are standard ones (e.g., equals and hashCode).
| # | Test | Can ever be | generated?Midterm Exam1代写 | If yes, | what outcome? | |
|
1. |
Lock l = new Lock(); l.acquire();
l.release(); |
A. Yes |
B. No |
1. Discards |
2. Reports |
3. Adds |
|
2. |
Lock l = new Lock(); int s = l.getState(); if (s == 0)
l.acquire(); |
A. Yes |
B. No |
1. Discards |
2. Reports |
3. Adds |
| 3. | Lock l = new Lock(); l.release(); | A. Yes | B. No | 1. Discards | 2. Reports | 3. Adds |
|
4. |
Lock l = new Lock(); l.release();
l.acquire(); |
A. Yes |
B. No 期中代写 |
1. Discards |
2. Reports |
3. Adds |
|
5. |
Lock l = new Lock(); l.acquire();
l.release(); l.acquire(); |
A. Yes |
B. No |
1. Discards |
2. Reports |
3. Adds |
Dataflow AnalysisMidterm Exam1代写
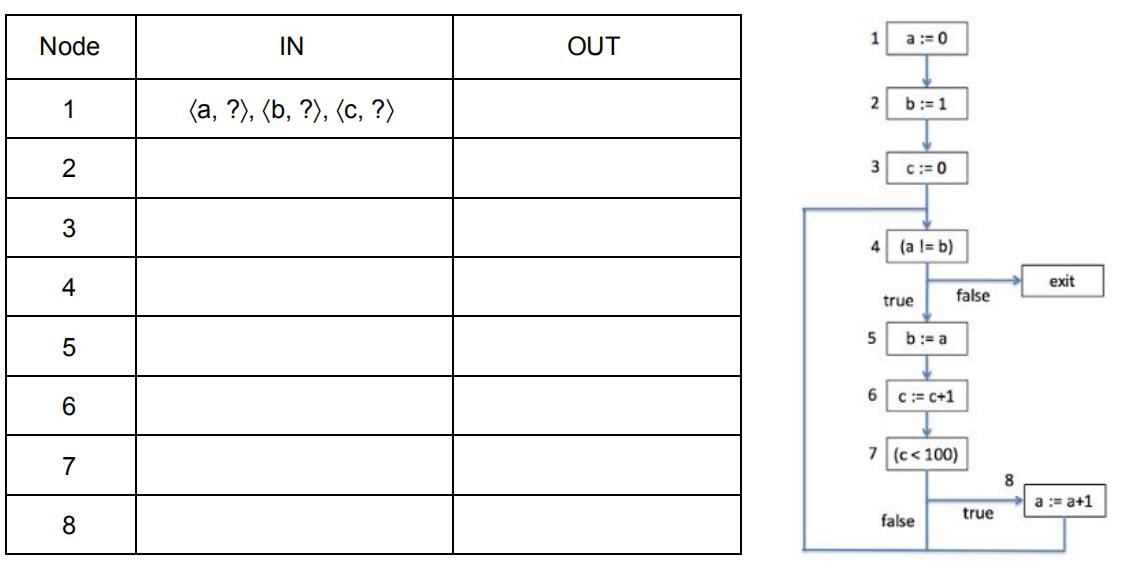
Question 9. Show the final result of performing reaching-definitions analysis on the given control-flow graph of the following program. That is, list the contents of IN[k] and OUT[k] for each k from 1 to 8.
a := 0; b := 1; c := 0;
while (a != b) { b := a;期中代写
c := c + 1;
if (c < 100)
a := a + 1;
}
Question 10. Answer the following questions about dataflow analysis for the simple WHILE language from the lecture on dataflow analysis.
a.The order in which the nodes in the control-flow graph are processed by the inner loop “for (each node n)” of the chaotic iteration algorithm can affect which of the following aspects of the analysis?期中代写
A.Soundness B.Completeness C. Performance D. Termination
b.What is the most efficient order in which to visit the statements in the below program (i.e., nodes in its control-flow graph) for a reaching-definitions analysis?
S1; { if (…) then S2 else S3 }; S4
A.S1, S2, S3, S4 B. S4, S2, S3, S1 C. S1, S4, S2, S3 D. S2, S3, S1, S4
c.What is the most efficient order in which to visit the statements in the below program (i.e., nodes in its control-flow graph) for a live-variables analysis?
S1; { if (…) then S2 else S3 }; S4
A.S1, S2, S3, S4 B. S4, S2, S3, S1 C. S4, S2, S1, S3 D. S1, S2, S4, S3
d.Suppose the given program has N statements (i.e., nodes in the control-flow graph) and V variables. How much memory does a live-variables analysis consume on this program in the worst case at any instant? Write the size of memory as an expression in terms of N and V. Give as tight a bound as possible. Remember that the analysis must store both the “in” and “out” information for each statement.
Pointer Analysis期中代写
Question 11. Consider a flow-insensitive, context-insensitive, but field-sensitive pointer analysis of the following program:
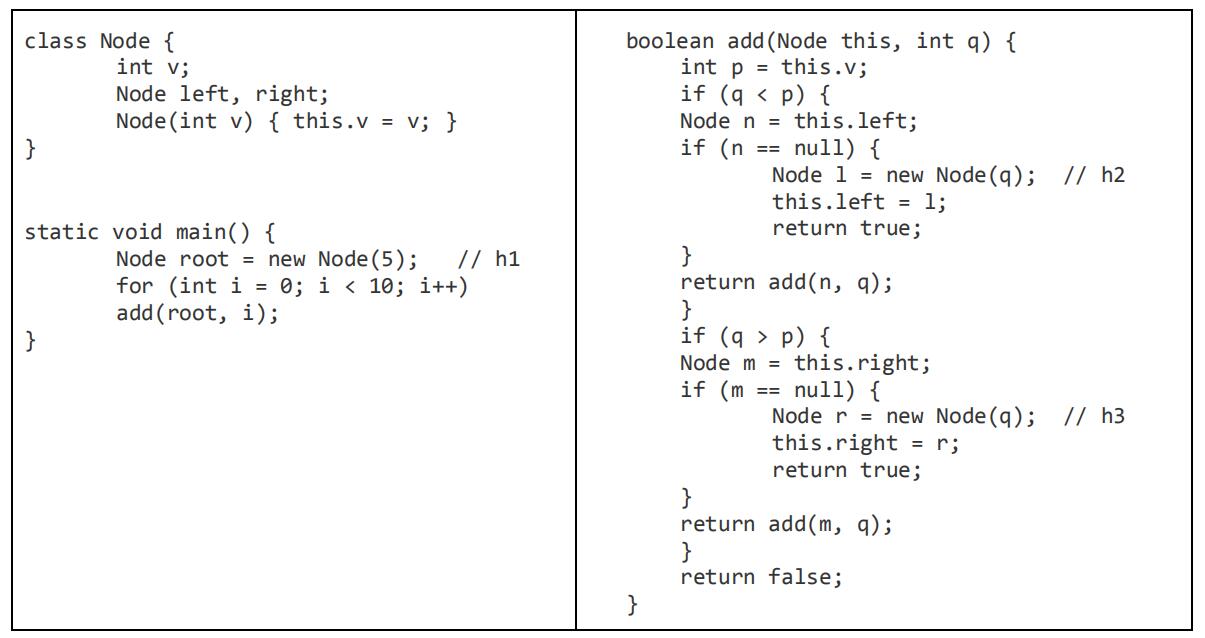
a.A flow-insensitive pointer analysis analyzes an (unordered) set of simple statements in the given program. Write the statements contained in this set for the above program (in the main and add functions together). Recall that this set includes only 4 kinds of statements: allocation (v = new h, where h is the commented label), copy (v1 = v2), field read (v1 = v2.f), and field write (v1.f = v2). The allocation statements are listed below for your convenience. You will lose points for listing statements not analyzed by this analysis.期中代写
Relevant allocation statements: root = new h1, l = new h2, r = newh3
Relevant copy statements:
Relevant field-read statements:
Relevant field-write statements:
b.For each pair of expressions below, write all correct choices among 1-3 below.
- They do NOT point to the same object in any (concrete) run of the program.Midterm Exam1代写
- The above pointer analysis proves using allocation-site based heap abstraction that they CANNOT point to the same object in any run of the program.
- The above pointer analysis proves using the type based heap abstraction that they CANNOT point to the same object in any run of the program.
A.root, root.right 1 2 3
B.root.left, root.right 1 2 3
C.root.left.right, root.right.left 1 2 3
D.root.left.left, root.right.right 1 2 3
E.root.left.right, root.right.right 1 2 3
F.root.left.right.left, root.right.left 1 2 3
其他代写:考试助攻 计算机代写 java代写 algorithm代写 代写CS function代写paper代写 r代写 金融经济统计代写 matlab代写 web代写 数学代写 金融经济统计代写 essay代写 java代写