CS33: Introduction to Computer Organization
计算机组织介绍代写 Question 1. Linking (4 pts)Suppose src1.c and src2.c are compiled and linked separately. Determine if the following combinations of ···
Notes:
- There are 75 points total, but the exam is graded out of 60. (ie. the exam is pre-curved so that there are 10 extra credit points possible)
- You may ask for questions on Piazza (private posts only). Clarifications will be posted to this google drive link: so it may be a good idea to check this before the exam is over.
- If the architecture of the machine is not specified, assume that the question is being asked in the context of a 64-bit little endian x86 machine.
Question 1. Linking (4 pts) 计算机组织介绍代写
Suppose src1.c and src2.c are compiled and linked separately. Determine if the following combinations of source files would cause errors, and if not, what would get printed.
Feel free to solve this problem by compiling the source files and linking them together. If an answer is undefined, simply write “undefined” in the result box.
| src1.c | src2.c | Result?
(“compile error”, “linker error” or describe output) |
int i=1; int main() { printf("%d\n",i); } |
int i=2; int func() { i=3; } |
|
int i=1; int main() { printf("%d\n",i); } |
int i; int func() { i=3; } |
|
int i; int main() { printf("%d\n",i); } |
int i; int func() { i=3; } |
|
int i; int main() { printf("%d\n",i); } |
int i=2; int func() { int i=3; } |
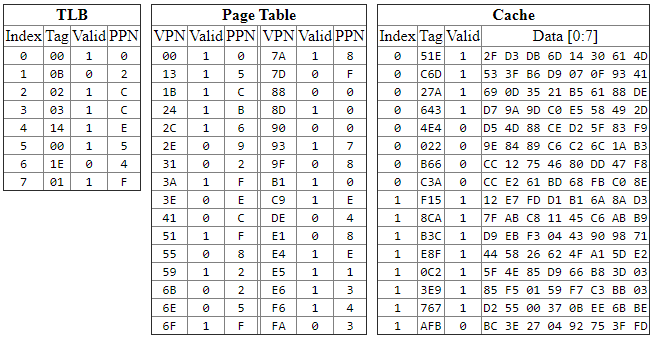
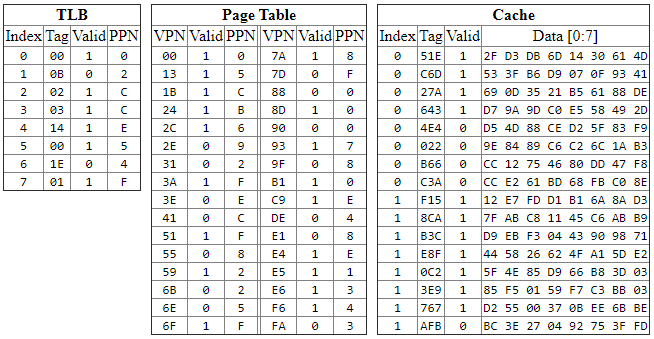
Question 2. Virtual Memory (6 pts)
Given the following details about the memory system and the states of the TLB and Caches, fill out the following information for a request for the virtual address: 0x597A0
- Main memory is 64 KB (2^16 bytes), byte-addressable with a 16 bit physical address.
- Virtual address is 20 bits long
- A page of memory is 4 KB (2^12 bytes)
- Direct mapped TLB with 8 entries
- 8-way set associative cache with 16 lines and cache block of 8 bytes
 0) {
0) {
printf(“D”);
}
}
}
else {
printf(“E”);
exit(0);
}
printf(“R”);
return 0;
}
1.List all possible program outputs (just put a space between answers if there is more than one, leave empty if nothing can be printed, 5pts):
2.Will there be any zombies after this program runs? (yes or no, 2pts)
Question 6. Multiple Choice (16 pts) 计算机组织介绍代写
For the following multiple choice questions, select all that apply. Ie. if none of the answers are correct, simply leave the question blank. (2pts each, no partial credit)
1.
What is the difference (or differences) between a TLB and on-chip cache?
a. The TLB is direct-mapped, while caches are set associative.
b. The TLB is indexed by the virtual address, while caches are indexed by the physical address.
c. The TLB stores virtual-to-physical address translations, while caches store data.
d. The TLB can be slow, but caches need to be fast.
e. The TLB stores instructions, while caches store data.
2.
Say we have two mutexes, implemented with binary semaphores, and two threads which access them. Which of the following can cause deadlock:
a. The threads lock the mutexes in the same order.
b. The threads lock the mutexes in a different order.
c. The threads unlock the mutexes in the same order.
d. The threads unlock the mutexes in a different order.
3. 计算机组织介绍代写
Which stack protection techniques are vulnerable to return-oriented programming?
a. Stack Canaries
b. Address space layout randomization
c. Limiting Executable Code Regions
4.
In malloclab, several students implemented an optimization where small blocks would be allocated at the beginning of a free block, and large blocks would be allocated at the end of a free block. In what way was this useful on some traces?
a. It increases the memory utilization due to less internal fragmentation.
b. It increases the memory utilization due to more coalescing opportunities.
c. It increases the throughput due to smaller free lists.
d. It increases the throughput due to better temporal locality in caches.
5. 计算机组织介绍代写
After a fork(), to access which datastructures should the resulting two processes synchronize?
a. Heap
b. Stack
c. Registers
d. Globals
e. Program Code
6.
What’s the purpose of the calling convention?
a. Enables virtual memory.
b. Helps enable separate compilation.
c. Improves external fragmentation.
d. Lowers the cost of creating threads.
7. 计算机组织介绍代写
Which of the following statements about C datatypes for x64_64 is true?
a. A float can represent any number a double can represent.
b. A double can represent any number an int can represent.
c. A char can represent any number a short can represent.
d. A long can represent any number a float can represent.
8.
Which of the following do not necessarily involve exceptional control flow:
a. Context switch
b. Killing a process
c. Page Fault
d. Function Call
e. Segmentation Fault
f. Timer Interrupt
g. Data Cache Miss
h. TLB Miss (in x86_64)
Question 7. Jumbled Metaphors (5 pts) 计算机组织介绍代写
As you reach the later stages of the exam, you may notice your mind becoming a jumbled pile of mixed metaphors. Sort yourself out by finding 10 words related to this course in the mess of letters below.
Rules: Words must be contiguous, and they may be forwards or backwards and either horizontal or diagonal. One example is given “thread”, but don’t count this one! Don’t list extra words, or we won’t grade the question. : )
Please List 10 Other Words Here:
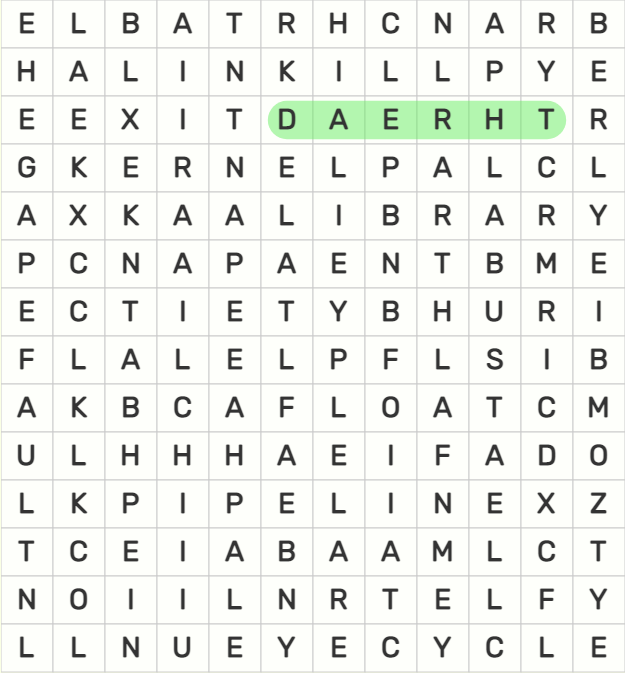
| pipeline | float |
| link | rpi |
| exit | library |
| api | rsa |
| cycle | kill |
Question 8. Soulmate Simulator (9pts)
Suppose we want to create a soulmate simulator, where we randomly compare exactly two people to see if they should be soulmates. For fun, let’s represent each person as a thread. We will call the “meet” function with many threads, and they will “mingle” to see if they are soulmates. The only important thing for this problem, is that there should only be two threads in the mingle() function at one time.
| Wrong Code | Your Code |
int number_of_people_meeting=0; void *meet(void *personID) { //This loop tries to ensure // there’s only one thread waiting while(number_of_people_meeting >1) { // do nothing } number_of_people_meeting++; //This is where we check for soulmates //between threads. mingle(); //We want at most 2 threads here! number_of_people_meeting--; return NULL; } void main() { pthread_t t[N]; for (i=0; i < N; i++) // make threads meet pthread_create(&t[i], 0, meet,(void *)i); } |
1.Examine the “Wrong Code” Above. In as few words as possible, why can’t it guarantee that only 2 threads are in the mingle function at the same time? (3pts)
2.Using a counting semaphore, complete the code on the right to guarantee that only 2 threads are calling mingle at the same time. (6pts)
Question 9: Inopportune Overlap (7 pts) 计算机组织介绍代写
Think about the following two cases of “overlap” between aspects of the virtual memory system.
1.Overlap of Variables -> Cache Lines:It’s possible to imagine that a single primitive variable (eg. int,float,char) could “straddle” two different cache lines. (ie. if it starts at the end of one cache line, and is long enough to proceed into the next cache line).
This complicates the hardware, because a single access to a variable from the CPU has to combine the information from multiple cache lines (yuk!). However, unless you are messing about with pointer arithmetic, this does not happen in C.
In as few words as possible, what aspect of the C language prevents a single primitive variable (ie. int, float, char, pointer, etc.) from being mapped to multiple cache lines? (2pts)
2.Overlap of Cache Lines -> Pages:It’s possible to imagine that one cache line could “straddle” two different virtual memory pages.
2.1. In as few words as possible, list one reason why, if this was possible, it would complicate the hardware or software for address translation. (2pts)
2.2 However, cache line’s don’t straddle virtual memory pages in real systems, why? (2pts)
Question 10. Another Phase? (8pts) 计算机组织介绍代写
OMG another bomblab phase? Using instructions we never learned in class? ���
00000000005858a8 <string_cmp>: # compares two strings, returns zero if equal #... asm omitted… (same as strcmp) 00000000005858b6 <string_cpy>: # copies string (same as strcpy) #... asm omitted... 00000000005858c4 <phase_defused>: #prints phase_defused message #... asm omitted... 00000000005858de <explode_bomb>: #prints explode_bomb message #... asm omitted... 00000000005858f8 <phase_11>: 5858f8: 48 83 ec 18 sub $0x18,%rsp 5858fc: 48 89 fe mov %rdi,%rsi 5858ff: 48 8d 7c 24 08 lea 0x8(%rsp),%rdi 585904: e8 ad ff ff ff callq 5858b6 <string_cpy> 585909: f3 0f 10 44 24 08 movss 0x8(%rsp),%xmm0 58590f: 0f 2e 05 12 17 09 00 ucomiss 0x91712(%rip),%xmm0 #Addr: 0x617028 585916: 7a 16 jp 58592e <phase_11+0x36> 585918: 75 14 jne 58592e <phase_11+0x36> 58591a: b8 00 00 00 00 mov $0x0,%eax 58591f: e8 a0 ff ff ff callq 5858c4 <phase_defused> 585924: bf 00 00 00 00 mov $0x0,%edi 585929: e8 22 df 00 00 callq 593850 <exit> 58592e: b8 00 00 00 00 mov $0x0,%eax 585933: e8 a6 ff ff ff callq 5858de <explode_bomb> 585938: 48 83 c4 18 add $0x18,%rsp 58593c: c3 retq 000000000058593d <main>: ... asm omitted... 000000000058595a <secret_phase>: |
Some helpful things:
- (gdb) print *(float*)0x617028
$3 = 1157837119180632802476425216.000000
- Ucomiss compares two floating point values, it works similarly to cmp.
- string_cmp is the same as the standard strcmp, and string_cpy is the same as strcpy, but I’m using my own versions b/c it makes the code easier to read.
1. What string will diffuse this phase? (4pts)
2. What string will enter the secret phase? (4pts)

更多代写:Nodejs代写 Financial代考 英国Proposal写作 Essay Claims代写 公共关系学paper代写 留学申请CV代写